 This is the second in a series of information war-gaming posts. The content of each post in the series will be determined by the discussion that follows the previous post.
This is the second in a series of information war-gaming posts. The content of each post in the series will be determined by the discussion that follows the previous post.In other words, I have no precise idea of what is coming next.

In the comments to last week’s “War-Gaming in Cyberspace” post, A Jacksonian had this to say (in part):
Not only is the MSM a vast wasteland of carrying pain and ‘feel goodism’ of everything being exactly equal, but government that is centralized and unaccountable is then beholden to those that can leverage power via threat and coercion. That is why extremist minority organizations target governments first — it has the power of punisher and it is that power that they want.
Information warfare in this arena is difficult, but not impossible, as the ’net yields asymmetrical tools, if you think about the internet as a tool and not just a message transportation system. As a tool system the internet is discriminating: multiple cultures and languages interoperate but rarely overlap beyond cross-over points. Thus, in larger, common MSM you will see a wide message given on a one-to-many paradigm and to do that the message must be simple and repeated multiple times as the cost barrier for rich information interchange is not present. What the MSM cannot do, and something that it will have problems tracking, is the concept of a many-to-many information system. These are described as a ‘Friend of a Friend’ or FOAF, and they are highly used by organized crime and terrorist organizations because they are ‘trust networks’. The positives of FOAF systems are: high degrees of internal trust, low degrees of penetration, and low degrees of outside interference due to the first two.
Putting these into a COIN paradigm, the methodology of going after the problem is, like in Iraq, not addressed at the highest scale first but at the lowest scale. National governments are too far out of the decision loop (or OODA loop) to be able to respond to anything but long, long term massive threats or immediate military ventures. The last place you want to venture for positive reinforcement of messages is National government and the best that can be hoped for is holding it to keep message systems absolutely open to everyone… whenever government bias is seen or encountered or promulgated it must be given high visibility and denounced. But you cannot do that as single individuals what is needed are internal nets of trust networks.
Yes, steal a page out of the other guy’s playbook and utilize the exact same outlook and methodology as it is effective. Then you do the one thing the enemy cannot do: apply it locally in the language discriminating parts of the internet that do not cross-operate well. These are havens that are language-dependent and should be a source of localize support and networking. The primary use of such networks cannot and should not be political — that is a secondary function given the Tom Paine paradigm of society. What it is good for are those things that support society, tradition, and keeping faith within trust networks between individuals and the local society as a whole.
The #1 weak point of modern societies is that of cutting off the modern from the past. By seeing the past as barbaric, backwards and quite nasty, the negative emplacement of those ideas by individuals supported by government is a continuous problem. From schools to the MSM to localized political groups espousing ‘progressive’ views, past culture is being removed from the modern culture and with that goes the direct support of the modern culture. By making it without attachment, culture can be molded into different forms, the worst of which is unable to stand for anything. If the modern West and other societies depending upon Western cultures cannot identify what they are then the entirety of those societies is up for grabs for those that can coerce government to do its bidding.
A Jacksonian has outlined the exact characteristics of the network needed to fight the information war against the Great Jihad.
Our governments are all but useless in waging this aspect of the conflict, being huge, unwieldy, slow to respond, tied up in red tape, and hobbled by political correctness. By the time any government understands the nature of this information war, the new Caliphate will already be in place.
It’s very difficult to turn our minds away from our central governments. We are long accustomed to looking to them for information, instructions, and solutions. But in our current struggle, not only is the government of no help, it is an active impediment to success.
And not just our governments. No large, centralized, hierarchically organized bureaucratic structure will be of any assistance against the worldwide networks of mujahideen. Anything that follows the government model — corporations, large religious groups, national charities, political parties — will exhibit the same inadequacies as our governments. If it has a head office and a chain of command, then for our purposes it’s useless.
The model of a hierarchically organized command network looks like this:
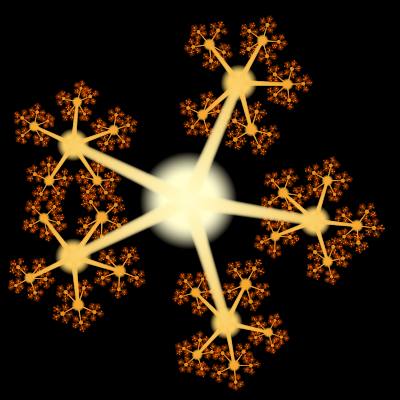
As you can see, it has a fractal nature, exhibiting an organizational structure similar to that of a central nervous system, or a lung, or the flower clusters of a butterfly weed plant. Hierarchical branching fractals of are found throughout nature, in both organic and inorganic systems. Wherever a flow gathers and aggregates into fewer and fewer channels, or is broken up and successively dispersed, a hierarchical structure will form.
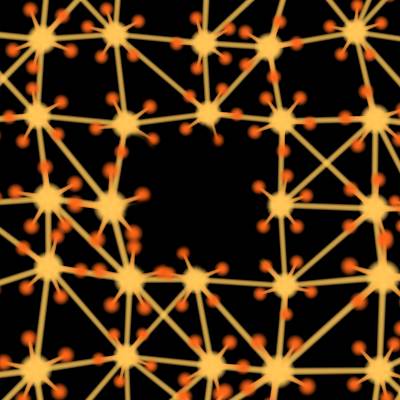
But other organizational network structures are possible, and are quite common. The one we are looking for is a flat or distributed network. It’s what A Jacksonian calls a FOAF network, and looks like this:
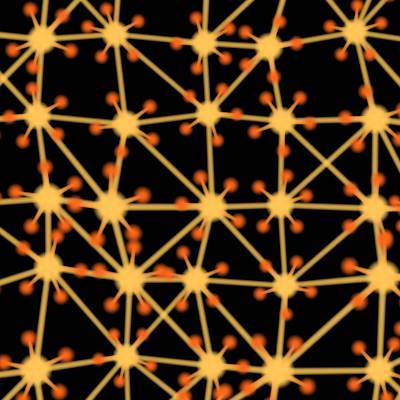
A familiar example would be a collection of small towns within a given region connected by road, rail, and the power grid. A prairie dog colony provides another analogy, with its separate burrows joined to one another by narrow tunnels.
- - - - - - - - -
In terms of social organization, the model for a hierarchical network would be the Catholic Church, with the Pope sitting in the Vatican in the heart of the central node. In contrast, Baptist churches form a more distributed network, with individual churches occupying more or less the same level, without answering to a command node.
 If a hierarchical organization is exemplified by the central nervous system of a vertebrate, a distributed network is best represented by the nerve net of a hydra, which wraps itself throughout the structure of the animal without ever forming a branched fractal structure or aggregating into ganglia.
If a hierarchical organization is exemplified by the central nervous system of a vertebrate, a distributed network is best represented by the nerve net of a hydra, which wraps itself throughout the structure of the animal without ever forming a branched fractal structure or aggregating into ganglia.The vertebrate central nervous system has proved the more successful in Darwinian evolution, so it obviously has its advantages. But distributed networks are still well-represented in biological systems.
From time to time they may even prove crucial to survival. We are currently at war with an enemy which has formed very effective distributed networks and is defeating us handily with them. We will be victorious in the current struggle only if we form flat networks that are at least as effective as theirs.
One way or another, it will be a distributed network that wins.
Why is it that decentralized non-hierarchical information systems are proving so effective now, after all the centuries in which centralized bureaucracy has been in the ascendant?
The primary explanation is the nature of modern electronic communication systems. Within an environment in which communications are slow and unreliable, the centralized model has all the advantages. In the hierarchical design shown in the diagram above, there is a maximum of ten connecting links lying between any two given nodes in the network.
The distributed model, on the other hand, may require many more intermediate links — hundreds or even thousands — to connect a given pair of nodes. When communication is by courier, or pony express, or even by postal truck or telegraph, this method is unworkable, and is easily defeated by a reliable hierarchical model.
But with almost instantaneous electronic communications over a worldwide network — cell phone, internet, radio, and so on — the advantages of a hierarchical system are lost. When all messages have to pass through a central node, the system chokes at the command point. In contrast, distributed structures in a flat network can form, emerge, perform their mission, and disappear in less time than it takes for a presidential memo to make its way from the Oval Office to an assistant undersecretary of defense.
That’s how Al Qaeda gets inside our informational OODA loop and stays there.
Another advantage of a distributed network is its ability to sustain and recover from damage. Depending on how close it is to the center, the removal of a node in a hierarchical network can cause major disruptions:
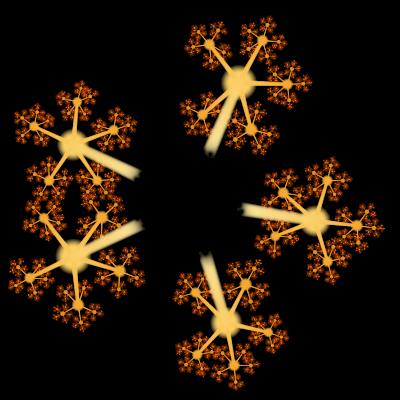
As you can see from this example, removal of the central node isolates the five sub-networks and makes them autonomous. In order to re-establish the full network, one of the sub-nodes must reconnect with the rest and assume supremacy over the others.
Removing a node from a distributed network causes much less of a disturbance:
The remaining nodes are analogous to routers in a computer network, and will find the most efficient route around the gap. As soon as a few new links form across the gap between the neighboring nodes, the architecture of the network will be restored, and will remain essentially unchanged.
How does all this apply to the Counterjihad?
Obviously, the nature of communications among real human beings is far more complex than the models described above. But for our purposes, the added layers of complexity only increase the advantages enjoyed by the distributed model.
Increased complexity tends to add layers to a hierarchy, thereby making it even more ponderous and unwieldy. The president adds a new cabinet department; a corporation creates a new layer of middle management; archbishops are inserted between bishops and cardinals in the organizational charts. The bureaucracy becomes more and more sclerotic and resistant to change.
The biological analogy would be the nervous system of the brontosaurus, in which three full seconds were required for a nerve message to travel from tail to brain and back again.
In contrast, adding complexity to a distributed network allows it to become more flexible through self-organization. Prior to instantaneous electronic media, networks were constrained by physical location. Nowadays they can be self-selecting within the entire global communications system. Like-minded people can discover each other, share functions, and create nodal links that amplify those functions.
These things are already happening. None of us has to be conscious of the process or direct it in order for it to occur. The nerve net of the hydra emerges naturally and performs its functions without any of the neurons involved planning what happens.
In fact, any attempt at conscious direction within the network will tend to convert it into a hierarchical system in which orders are given and carried out along a chain of command.
If we choose to inhabit a distributed network, a global overview is all but impossible to achieve. Our understanding of the entire system will of necessity remain within the realm of analogy and metaphor.
What each of us can do from within our limited perspective is to learn how to contribute more effectively to the immediate environment of our network. We can recognize our own abilities and utilize these talents to build stronger links to our neighboring nodes. It’s not necessary for us to know and understand what goes on in the distant regions of the network, but we can become adept at functioning in our chosen local environment.
Later posts in this series will cover more specific applications of distributed networks to our information war. But there’s one thing we all should remember: the architecture of our networks is always mutating. Nothing we plan for should assume any permanency. The only constant is continuous change.
One of the changes that may lie ahead is that we will be forced underground. Right now, even though I blog anonymously, I can communicate and organize relatively freely here in the USA. But in some European countries the things I do and say are already illegal, and it may not be long before the same restrictions emerge in the United States. Mark Steyn has recently discovered the chain-link fence that surrounds “free” speech in Canada.
Each of us should be prepared for an internet crackdown, and any organizing we do should allow for alternative means of maintaining our networks. The old ways are slower and more cumbersome, but if we build them wisely, when the time comes they will suffice.
45 comments:
A couple immediate thoughts to this useful post...
1. Our adversaries understand the sclerotic nature of our governments and media, and are infiltrating them from within. ISNA, CAIR, MAS are using the hierarchical model to meet with the DOJ, Homeland Security, DoD (not to mention State Dept and CIA, lost long ago to the Saudi petrodollar "retirement augmentation" tactic) and to neutralize or actively redirect the missions of those organizations regarding Islamists. Hierarchical organizations may be slow to change, but they still enforce existing laws, and new laws being drafted by CAIR et al for the 2008 Congressional session. So although hierarchies are incapable of protecting the American people at times, they are very vulnerable to infiltration used to subvert American interests, Constitutional liberties and simple national self-preservation.
2. John Boorman's "The Protracted Game," published back in the late 60s, is a useful model for combining hierarchical and distributed networks applied to warfare - he uses the historical experiences of Mao's early tactics within the context of the Chinese game of Go (Go standing in here as an abstraction of distributed networks). This book is always a useful resource, I've found, for suggesting useful ways to think about current problems - I often return to it. It is as much a solace as Boethius' Consolation of Philosophy.
One might even conceive of the problem as a combined game of chess and Go, where chess has a hierarchical set of rules, and Go of course is supremely egalitarian and distributed where each piece operates with equal powers. Territory - boardspace - becomes mindshare, or our ability to control the memes. We've corresponded on this - that article on apply the Lokta-Volterra equation to competing memes.
Is it possible that using both kinds of network topologies - centralized and also decentralized - and understanding the complexities of the interplay between them is actually a closer reflection of how the game is really played?
And so - to present a use-case and reduce all this abstraction of game theory to an example - that we would look at a situation where hierarchies are needed in order to effect specific actions, such as drafting and passing legislation through centralized hierarchical work, but supported by decentralized FOAF grassroots pressure that pushed the hierarchy to vote a certain way ?
And the next question - just for my train of thought - would be which issues are most important for this kind of combined scenario construction?
Networks differ in a number of important ways. For instance, many are 'small worlds' that are scale free. The Internet is to some degree this kind of network as are many social networks. A scale-free network of this sort has a lot of small sub-nets that are highly linked, but the linkages between sub-nets are much more sparse.
When considering how to attack our enemies' networks, it's critical to distinguish these sorts of relationships between people and groups. For instance, using publicly available data, the Kenya embassy bombings were executed by a small local sub-net whose connection to the Al Qaeda sponsors was through one thin personal link. That makes this sort of network hard to stop - unless you can identify and remove the critical nodes.
There's a whole new discipline of network science that is emerging. The US Army is sponsoring a lot of it with regard, not only to social networks, but also to infrastructure etc.
Of course, the Kenya cell suggests some possibilities for anti-jihad and anti-information warfare strategies of our own.
For instance, while it can be useful to have high profile spokesgroups getting TV time and political attention, such groups are vulnerable to e.g. Saudi-financed lawfare attacks.
Combine such groups with hundreds of blogs, with letter writing by thousands of citizens not only to politicians but to newspapers, and you have a traditional political / issue campaign.
But post scathing videos on YouTube and elsewhere, including on multiple anonymous servers with links to the videos from hundreds of bloggers, and it becomes much harder to shut down.
Administrative 'nodes' that are subject to correct censorship, corruption, and or extortion are vulnerabilities.
Google Blogger is one such example .
There's more than one freedom of speech advocate rotting in a Chinese jail thanks to Google. (and Microsoft, and Yahoo)
Excellent post and comments.
I have been negligent in reading this site, an oversight that will be corrected.
Hi all,
I hope this thread does not die, since I would like to present a small proposal here.
Let us imagine an online system which would publish counterjihad news not in a form of a blog, but in a form of a PDF ready-to-print. With some basic knowledge of typesetting, one could relatively easily create a piece of software that would assemble several news and images into a viable leaflet. This leaflet could be regularly (or irregularly) updated with fresh stories etc., and would contain some WWW addresses with prominent counterjihad blogs.
Now imagine that this PDF is distributed to anonymous volunteers, who are willing to print it on their home printers, and distribute some of them: some of them using classical snail mail, some of them, perhaps, by sticking the leaflets right into the postboxes. I think that one volunteer could distribute ~ 200 pieces monthly without having to pay too much in money and time.
In fact, this could be reasonable task for younger members of patriotic parties, not only in Europe, but also India, Thailand ... in bigger communities, they could create their own language mutations (like Danish or Flemish), with regionally important news.
In this way, we could perhaps attract to counterjihad people who would otherwise never meet any counterjihad blogs, because they do not spend as much time on the internet as we do.
Marian has a point.
Whatever is included MUST be well referenced-It cannot appear to be a "propoganda" pamphlet.
But what market to reach for?
The target that needs "conversion" is the idiot moderate, the person who manages to be undecided 10 days before an election. The person who accepts PCism without really thinking about it, and so may be swayed. People you don't understand the term "Dhimmitude", and would be horrified to learn about it.
Marian,
One of the signs that your idea is a good one is that at least two other people have thought of it independently. That makes it a "meme with a distributed emergence", which indicates to me that its time has come.
I'm calling it the "Sticker Project", and have thrown it open to people at CVF for suggestions about how it might be implemented.
Digital samizdat.
Be aware that the US and perhaps European authorities already are tracking the jihadi darknet - some of which operates in just the ways described above, i.e. with pdfs, steganographic encoding of information within music and photo files etc. as well as with standard web pages. Don't assume they can't find or won't track a similar darknet from the counterjihad such a net should be seen as posing a threat.
The military doctrine of 'defense in depth' is worth thinking about. Don't assume any single defensive part of the system will hold. In fact, assume that ANY part of it can and eventually will be breached.
The aim is to use sufficient layers of these to make it not timely or cost effective to do so in most cases.
*if* such a net should be seen ....
What about the attempt to kill ALL nodes in one fell swoop?
UN moves to kill free speech, passes resolution against "defamation of religions"
It took the cultural Marxists, following Gramsci's Long March strategy, ca 40 years for their initial breakthrough into Western society (1925-65), and another 30 years to gain full control of the 'commanding heights' of Western civilisation. It took the Islamists, starting several decades later, a similar amount of time to establish themselves in the West; first gaining control of the mosques, then infiltrating the government bureaucracies and media. Islamist influence on the bureaucracies is still fairly limited and dependent on the support of the cultural Marxists, who do now largely control the hierarchies.
One thing that concerns me is that you seem willing to cede control of the hierarchies (FBI, education system, military etc) to your enemies. This seems like a mistake considering that most police men, soldiers, and even many govt bureaucrats, are still basically on the side of the West. Perhaps you should focus on getting your message to such? Especially to mid-ranking persons with prospects for promotion.
Baron
As I do not see any flat network existing at the moment that is capable of taking on a Jihad net, except the one of Baptist churches, are you suggesting that this, and other such Protestant Christian church networks, are practically the only usable ones we have at the moment.
I can see several advantages.
Christine:
An appalling example of the infiltration you describe in item 1 of your post may be seen in a story in the Dec. 28 Washington Times on the activities of Gordon R. England, a deputy secretary of defense. An excerpt:
"Mr. England has been a leading advocate of what critics in the Pentagon say is a misguided attempt to reach out to the wrong Muslims, regardless of their views, in an effort to counter Muslim extremism.
"That approach has kept military and civilian officials from conducting much-needed assessments of how Muslim extremists are waging war because doing so would involve analysis of Muslim religious tenets, a politically taboo subject area." (Emphasis mine.)
For what it is worth.
The jihadists have a core ideology to which they can refer: the Koran; the counter jihad does not. Jihad is the personal duty of every believer. The mooselman, once trained- indocrinated, does not have to confer with the local imam re his personal jihad.
The Communist/socialist: the liberal had/has a similar position: he just needed to know the ideology. He is then free to incarnate the socialist dogma within his field of expertise or discipline. There was, as in the 60's revolution, a cadre that kept discipline and correct dogma.
The communist/socialist/jihadist also form cells; or liberals form non-profits to NGOs.
The Counterjihad does not have a core doctrine or even philosophy: previous articles on this site have even touted that attribute of the counter jihad. It therefor cannot train and disseminate doctrines that the individual can incorporate into his discipline.
The communist/socialist was enabled by the concept "there is no enemy to my left". There is no such similar concept on the right: Newt Gingrich was more severe towards his right-wing critics than his left-wing opponents. The guardians of the Conservative movement are prone to read perceived political deviants out of the movement: reading National Review in the 60s - 90s left me with the thinking that Protestants weren't welcome.
The counter jihad will be perceived as a more dangerous threat than the actual jihad. The counter measures taken will be more aggressive domestically and there will not be social structures in place to protect us: lawyers will not spring to our defense; the ACLU will not be silent. There will not be any friendly U.S Attorneys as Debbie Schussel reports there are for Muslims.
My suggestion follows on what I wrote in the previous thread: begin the "long march through the institutions". Create interlocking NGOs with their ubiquitous press releases and studies. Take over Conservative institutions by flooding their memberships. Create sources of funding in imitation of Soros and Saudi Arabia. Make use of campus ministries: this is a religious war as well -- educate fellow Christians. If you're in position to hire for any such group, manipulate the process in favor of the counter jihad.
Vol-in-Law --
Yes, I have ceded the organizational structure of these entities to the enemy. But not all the people who inhabit their hierarchies, particularly at the lower levels. They are the folks at whom I am ultimately aiming.
The regular people who inhabit the lower levels of the bureaucracies are already members of other distributed networks, the churches, for example, as DP111 points out. Many of them still have principles and love their country. I believe that they can be part of the solution.
As Christine pointed out, the FBI, the State Department, and other federal entities are already compromised. They have been corrupted from the top downwards by all those golden Saudi parachutes that have been lavished so shrewdly by the Wahhabists and their cutouts.
We're in a worse mess than a lot of people realize, and the Republican party is only slightly less corrupted than the Democrats.
DP111 --
There are other flat networks available to the Counterjihad besides the churches. The churches are older and more visible, but there are other organizations, and new ones are forming all the time.
It may take some looking beneath the surface to find them, but they are there.
NJArtist --
The Counterjihad does not have a core doctrine or even philosophy: previous articles on this site have even touted that attribute of the counter jihad.
If I ever touted such an attribute, it was a grave mistake on my part. I think you will find any number of posts in which I outline the core of what we are fighting for. I was posting essays on the topic almost three years ago; check out Naming Ourselves.
But your "long march through the institutions" strategy is a good one. Perhaps that's what we are beginning here.
What you are looking for is already beginning to happen. For example, conside that ordinary non-academic Swede who called into the radio show and gave the listeners a well-informed lecture on the evils of Islam.
There is a common comprehensive body of counterjihad understanding that circulates through all our blogs, websites, and talk radio. It is being absorbed and internalized by regular people all over the Western world.
The thing you are looking for is already happening. The trick is not to be mesmerized by the media when looking for it, and to remember that truly distributed networks never get even 15 minutes of fame.
I think we need to create a network of blogs that each support one technical area to support a grassroots counter jihad. This way folks can avoid being prosecuted in finland and germany, targeted by lawyers, how to expose their local jihadis and dhimmis etc.
We know that to be effective, we need to be organized, but in a decentralized way. I started a new blog under my current name (registered with Google using a russian email address, try and get a search warrant in russia, dearest George)and started to open threads along the lines of the "what we can do" items that I listed previously.
I realized that the subject area is too broad and too deep for a guy with a full time job to handle. If anyone would like to get involved, swing over to my blog.
How about this for the start of our "core document" (not meant to be exclusive of non-Americans) ?
"We hold these truths to be self-evident, that all men are created equal, that they are endowed by their Creator with certain unalienable Rights, that among these are Life, Liberty and the pursuit of Happiness. That to secure these rights, Governments are instituted among Men, deriving their just powers from the consent of the governed."
It's certainly un-Islamic and counter-Jihadic!
I have been advocating since 9/11 that the one thing we Americans can do to unite us as a country is to read the Declaration of Independence aloud at a gathering of friends, family, and neighbors each and every July 4. I have been doing this since 2002. Go viral - plan it now!
The reason I give the Paine twist to things is that he correctly intuited the ideas of the Declaration before they were written, and while his views were specific to the Colonies, they tended to describe orderly systems passing into disorder. His foundational view, from the US perspective comes from two small sections of Common Sense... first:
"Some writers have so confounded society with government,
as to leave little or no distinction between them;
whereas they are not only different, but have different origins.
Society is produced by our wants, and government by our wickedness;
the former promotes our POSITIVELY by uniting our affections,
the latter NEGATIVELY by restraining our vices. The one
encourages intercourse, the other creates distinctions.
The first a patron, the last a punisher."
This is, perhaps, one of the key foundations of Western society that has been absolutely ploughed under by socialism and its third generation communism, both of which seek to replace the society with government. That, however, has proven to have long-term weaknesses against commitment to ideology that is anti-thetical to it, as was the case with the Poles adhering to the Catholic Church and local community views. For all the outpouring of views against the USSR no one could take down the 'workers paradise' from the outside - only those with the hammers on the inside could do that. That had antecedants, but by the time of the Solidarity strikes, the structure was ripe for those blows.
Europe is currently undergoing that exact, same phenomena with the EU and is open to the exact, same type of return. While the Colonies saw a loss of external cohesion yet still having internal cohesion, Europe is gaining great layers of external cohesion meaning it is ripe for internal decohesion.
The next passage talks to the state of the Colonies just after Bunker Hill, but before the Declaration:
"The present state of America is truly alarming to every man who is
capable of reflexion. Without law, without government, without any
other mode of power than what is founded on, and granted by courtesy.
Held together by an unexampled concurrence of sentiment, which,
is nevertheless subject to change, and which, every secret enemy is
endeavouring to dissolve. Our present condition, is, Legislation
without law; wisdom without a plan; a constitution without a name;
and, what is strangely astonishing, perfect Independance contending
for dependance. The instance is without a precedent; the case never
existed before; and who can tell what may be the event? The property
of no man is secure in the present unbraced system of things. The mind
of the multitude is left at random, and seeing no fixed object before
them, they pursue such as fancy or opinion starts. Nothing is criminal;
there is no such thing as treason; wherefore, every one thinks himself
at liberty to act as he pleases. The Tories dared not have assembled
offensively, had they known that their lives, by that act, were forfeited
to the laws of the state. A line of distinction should be drawn, between,
English soldiers taken in battle, and inhabitants of America taken in arms.
The first are prisoners, but the latter traitors.
The one forfeits his liberty, the other his head."
The strong external force over the Colonies was now suffering a decohesion from the inside - the Colonies had a de facto revolution going on without the formal Declaration. This could not have been done without internally cohesive structures of society. When government loses affiliation and contact with society, there is a time when the individuals in society decohere from it and will no longer follow governmental law. This is extremely corrosive to authoritarian systems, but to have that you must have those internal, societal structures to start with. Not only are those structures resistant to external authority, they instinctively defend themselves from externally imposed ideology contrary to their culture.
The title of this blog points to just that time at the Gates of Vienna: all of Europe did not come to defend the Gates, but the stalwarts that recognized the threat to their culture did. In a distributed cohesive system that reacts, there are deep allowances for differences between associative groups and yet commonality on the idea that the society is worth protecting. And if government stands in the way or actually tries to stop it, THEN, just like in the US, you get the Declaration and the 'change or abolish' language.
Paine clearly dealt with the inalienable rights as they were present before his eyes. He would also come up with a self-governing system with similarities to what would finally come out of 1775-87 period. When dealing with multiple cultures in need of common defense, it is those within that system that will see the need to defend themselves *first* and regularize things *afterwards*.
Very messy!
Chaotic, in fact. But, like emergent structure, it is chaos with a purpose. Stick to the basic principles, organize at natural levels that are adaptable between organizations (one size does not fit all) and then utilize that structure that emerges. The Committees of Correspondence served much of that purpose prior to the Revolution so that ideas could be examined and either supported or removed from the system by general agreement.
Sections of Europe once had just such an organizational capacity: the Gates were held at high cost. It is those pockets of strength and adaptability that must be found, supported and promulgated... far faster than any legislature can do anything about them. That also means local community support and the erosion of localized systems to start freeing up communities and putting up culture against mere law. And these cultures had Varangians who came from much farther north trodding through the Middle East, once upon a time. That easily gathered defenders against encroaching and corrosive religious structures and demanded the right of individuals to be free to choose religion... and the Peace of Westphalia resulted after a horrific and bloody set of wars, but the point and freedom were won. From high didactic reasoning in Paris to the strong defender of Transylvania, Europe generated these cultures and the adaptability to *resist*. If those are *gone* so is Europe... I seriously doubt they are. Perhaps sleeping with the gentle poison of dependence that is perfection and lethal... but the heart of perfect Independence shifts that equation. Throw in the Feiler Faster Thesis and the 'net and small changes held and worked on begin large changes. America, itself, is slowly learning the horrific effects of perfect dependence, and we may just see a time where the nameless Constitution truly has no name once more.
Baron:
"Yes, I have ceded the organizational structure of these entities to the enemy."
In the strongest possible terms, you cede NOTHING to the enemy. NOTHING.
If it is of no use to you, you burn it to the ground and salt the soil with anthrax spores to deny him the terrain.
The point about the vulnerability of hierarchical organizations is well taken, but they DO have their undeniable strentghs.
Any deep-pocketed and deep-bench hierarchy focused on a few well-targeted nodes of a FOAF network will shatter the lateral links of the smaller network.
I give you the FBI vs. the KKK.
There is a very good reason why the Jihad targets the established governments...they must use those governments' resources and manpower against the majority to enforce the dhimmitude.
How we can influence the government to favorably effect the CounterJihad, in the American context, is demand the identities of the flunctionaries who set and enforce PC nonsense and other anti-Judeo-Christian policies.
A bureaucrat with a "face" is soon re-assigned to lesser duties.
Once identified, an unfavorable policy or legislation must subject the author, and his or her superiors, to an unrelenting barrage of ceaseless negative feedback and protest.
Even if the author of the poilcy isn't known, the blowback will eventually "come home to roost"...and the other drones will soon get the message.
Bill Clinton's Brady Law and Assault Weapons Ban and it's congressional aftermath come to mind.
Anything or anyone that does NOT serve the Counter-Jihad is a legitimate target. It serves, or may serve, our enemies, and if it cannot be turned to our ends, it must be destroyed root and branch.
"Inalienable Rights" beat me to it, but as islam has the Koran, we also have our core documents. They are the Declaration of Independence and the U.S. Constitution, with particular emphasis on the Bill of Rights. They are our strength.
As they said in "300" - "Give them nothing, take from them everything."
Bilgeman:
Ceding NOTHING to the enemy is precisely what brought Germans the Stalingrad defeat.
Everyone probably remembers what happened to the 300, albeit they made a great achievement.
In real warfare, one does not have enough resources to protect everything at the same time, and one needs to pick up more valuable targets of protection.
Doing otherwise makes a heroic last stand - which will be promptly removed from the history textbooks by the victors.
Marian-CZ,
Point taken on the last stand of the 300. But they did give the rest of their countryman time to prepare and eventually win. My intent was to show that in 300 they did not go to battle intending to "win the hearts and minds" of the enemy. They did not worry about being politically correct, or about what the press would say at home, or if they would be charged with murder for killing the enemy. They went to win.
I think we should have the same mindset.
Yes, we should pick our battles, attack where we can, but always with the mindset to WIN!
And, as most of you know, the "Fifth Column" in the U.S. is just as much an enemy as the terrorists abroad.
A deeper problem with the scorched earth approach is that the counter jihad struggle must be waged in our own communities.
We have to LIVE WITH the consequences of our actions.
Which is why I and many others will bitterly oppose anyone who blithely tosses around an intent to "salt the earth with anthrax spores".
So much here!
rkb-
The point of a successful counterjihad is to stop Jihad before it gets to our neighborhoods.
So, yeah, we can actively counter it in our environs before blood is shed.
________________________
Many very good ideas here and thanks to the Baron for bringing it to the fore.
I want to take just a moment and address those here who have given up on government. It's a very mixed bag right now and there's a lot to be pessimistic about but there are some opportunities, as well.
Romney has repeatedly used the word 'Jihad'--a move as controversial as Bush naming 'Islamofascism' a while back. Giuliani's co-chair for southern NH says (paraphrase here) 'no good or bad muslims--just Muslims'.
Thompson best of the lot for having comprehensive policies encompassing everything from energy to the border.
We must remember that vast portions of the Jihad are not distributed systems. That there are heads to chop. This is particularly true in the financial, litigational, media, and otherwar tactics.
We must continue to cut off funds and we've had some setbacks--notably the October Dallas decision re the Holy Land Foundation and Friday's 7th Court decision reversing a $156M award to an American killed in the West Bank by gunmen tied to Hamas.
I like Bilgeman's idea of witchhunts in agencies and Congress. But unlike the quote from Thomas Paine (and I'm a devotee--my blog is titled Your Daily Paine) I believe that instead of losing "his head" we should first pump vigorously for intel and then try to bring back to the Christian fold. This I learned from Jesus.
Now for anybody who's lost sight of the ball this still all comes down to money. Without their petrodollars Muslims would still be in their third world cesspools with no resources to expand into the civilized world.
So I want to state something I believe to be unequivicable. So long as we are energy dependent, so long as the billions flow from us to our enemies, there will be no end to the Jihad. WE are quite literally buying the rope.
And for all the hybrid and electric cars, for all the corn mash whiskey (what do you think ethanol is?) we are still dependent on oil and coal, and will remain so for the foreseeable future.
Distributed networks can do little to counter this particular problem. We need leaders that understand our energy needs are much more than just energy needs. Our energy independence is our single most potent weapon in the counterjihad and those that don't yet 'get it' better find out.
If that means turning Alaska and the continental shelf into Swiss cheese then consider me to be yodeling to beat the band. We have enough resources for ourselves and Japan.
So the best grass roots movements you or I can support are the ones that get the watermelons out of power and the grown ups in power.
Bilgeman: There is a very good reason why the Jihad targets the established governments...they must use those governments' resources and manpower against the majority to enforce the dhimmitude.
How we can influence the government to favorably effect the CounterJihad, in the American context, is demand the identities of the flunctionaries who set and enforce PC nonsense and other anti-Judeo-Christian policies.
A bureaucrat with a "face" is soon re-assigned to lesser duties.
Once identified, an unfavorable policy or legislation must subject the author, and his or her superiors, to an unrelenting barrage of ceaseless negative feedback and protest.
Even if the author of the poilcy isn't known, the blowback will eventually "come home to roost"...and the other drones will soon get the message.
Bilgeman is on the money. Previously, I had viewed Islam as the major threat. While it might be in the most immediate sense, the far greater enemy is Political Correctness. It is the AIDS infection that permits a much simpler virus like Islam to finally kill the host. Socialism, Political Correctness, Multiculturalism and Transnational Globalism are the four horsemen of the philosophical apocalypse that—given the opportunity—will disarm the West and throw open its gates to the barbarian hoards.
One critical step that may be needed is the elimination of all "hate speech" laws. They provide unequal protection under the law and are the result of prejudice within our enforcement agencies. Had the police and other law enforcement groups aggressively pursued all cases of verbal and physical assault against individuals of any stripe, there would be no need for categorized "hate speech" laws.
Such preferential treatment has allowed other pet liberal causes to become ensconced within our legal code. Gun control laws spring to mind as a solid example of this. Current attempts to pass laws prohibiting disparagement of religions and what such nonsense are the logical extension of this sort of legalistic mind control and need to be shouted down and ridiculed for the nanny-state politics they are.
Marian-CZ:
"Ceding NOTHING to the enemy is precisely what brought Germans the Stalingrad defeat."
I don't know what history you've read, but the accepted reasons for the 6th Army's defeat at Stalingrad was the decision to capture the city instead of bypassing it, the reliance on the Luftwaffe to resupply the encircled pocket, and the refusal by Hitler to allow Von Paulus to attempt a breakout to westward.
Fact of the matter is, Marian, the "Scorched Earth" policy served the Soviets well against the Nazis, the Russians against Napoleon, and if you've ever read of Mohammed's campaigns, the Prophet against his enemies.
(He'd fill in and befoul drinking water wells.).
"In real warfare, one does not have enough resources to protect everything at the same time, and one needs to pick up more valuable targets of protection."
I think you're assuming that the Counter-Jihad is not a "Real War" because we don't have uniforms, generals, or government-provided budgets.
In fact, the resources of the Counter-Jihad are unfathomable...precisely BECAUSE there is no formalized command and control structure.
And while you're quoting me von Clausewitz out of context,(destroying an asset, rather than leaving it for the enemy's exploitation obviates the need to defend that objective, see?), I'll retort with Napoleon:
"In Battle, the Moral is to the Physical as Three is to One.".
As the Jihad progresses, it will find each advancement 3 times harder than the last.
This IS the real war.
This campaign is aimed at creating a Jihadi "rational army"...(one that runs away...or never shows up in the first place).
The goal of information warfare is to render impossible the very ideas of aggression or resistance against you in your enemy's mind.
rkb:
"A deeper problem with the scorched earth approach is that the counter jihad struggle must be waged in our own communities."
If there is that in your community that is amenable to being used to oppress and enslave you, then I'd assert that it really ISN'T "your" community at all.
zenster identifies a very good target:
"One critical step that may be needed is the elimination of all "hate speech" laws."
If we cannot use these execrable pieces of legislation against the Jihad, then they should be dismantled so that they cannot be used,(as they already are being attempted to), against us.
"Which is why I and many others will bitterly oppose anyone who blithely tosses around an intent to "salt the earth with anthrax spores"."
You will opt to live on your knees rather than die on your feet?
"We have to LIVE WITH the consequences of our actions."
Perhaps, perhaps not.
It is just as valid, though, to observe that our children must live with the consequences of our inaction.
Fancy your daughter or grand-daughter in a burkah, or imprisoned in her own home?
This is happening in Europe today.
The consequences of people, apparently like you, who cavilled at doing what was necessary to prevent it.
I tell you that the cost of correcting such an environment is far worse than that required to prevent it.
A distributed network is important for producing resources (manpower, money, political weight etc.) but it offers no real strength with which to attack, therefore the distributed network should be seen as the safety net. It is only when a hierarchical network forms above the distributed network (not independently of – visualise a pyramid with bigger nodes higher up) can real action be taken.
How will the political weight formed in a distributed network be utilised without a hierarchical network to direct it.
Wat --
Ah, you anticipate me! I'm getting to what you want to talk about. Be patient; it takes time for this whole thing to unfold.
A distributed political movement -- e.g. a peasants' revolt -- can be very effective; you should know this better than most people.
But after the change occurs, a distributed system cannot govern. We must return to hierarchies if civilzation is to function.
This post only serves to highlight the fact that existing hierarchical structures in the West are all but useless for the task that lies immediately before us.
Baron:
"This post only serves to highlight the fact that existing hierarchical structures in the West are all but useless for the task that lies immediately before us."
Ahh, but in a democratic system, the underlying distributed network is what underpins and supports the hierarchy.
Are we not seeing exactly that in Geert Wilders picking up the banner from Pym Fortuyn?
The Cause is what is important, the figureheads can be replaced.
Bilgeman: If we cannot use these execrable pieces of legislation against the Jihad, then they should be dismantled so that they cannot be used,(as they already are being attempted to), against us.
An excellent expansion upon what I meant to convey. Bravo. Let's face it, if the UN is trying to pass a resolution prohibiting any disparaging of religion, then we'd do well to make sure that no such tommyrot infects our own legal codes.
Now imagine that this PDF is distributed to anonymous volunteers, who are willing to print it on their home printers, and distribute some of them: some of them using classical snail mail, some of them, perhaps, by sticking the leaflets right into the postboxes. I think that one volunteer could distribute ~ 200 pieces monthly without having to pay too much in money and time.
The PLO did a similar thing during the first intifada. They would daily pamphlet the public in Gaza as to how to respond to Israel, and it worked successfully. Thomas Hammes uses this example in his book.
We need carefully crafted (sticky - as Baron put it) messages that are well referenced.
So I want to state something I believe to be unequivicable. So long as we are energy dependent, so long as the billions flow from us to our enemies, there will be no end to the Jihad. WE are quite literally buying the rope.
Yes and no. The average Saudi prince has about 100-150 sons, so that oil wealth gets spread ever more thinly as time goes on, and Saudi princes are not known for living within their means. Read Baer's "Sleeping with the Devil." Sooner or later, there will be too few petrodollars to pay off the jihadists to not attack the house of Saud. Once that happens, oh boy. Already, various princes are resorting to extorting money out of shop owners and other racketeering to maintain the lifestyle they feel entitled to. It can't go on much longer.
A distributed network is important for producing resources (manpower, money, political weight etc.) but it offers no real strength with which to attack, therefore the distributed network should be seen as the safety net. It is only when a hierarchical network forms above the distributed network (not independently of – visualise a pyramid with bigger nodes higher up) can real action be taken.
How will the political weight formed in a distributed network be utilised without a hierarchical network to direct it.
The heirarchy is the SIOE, which is the brains behind the movement. The distributed network are the non-Islamic European peoples.
prcaldude-
Kingdom of Saud falls and is replaced by...Methodists?
So long as we transfer treasure to the ME, the Jihad is funded.
The average Saudi prince has about 100-150 sons, so that oil wealth gets spread ever more thinly as time goes on, and Saudi princes are not known for living within their means. Sooner or later, there will be too few petrodollars to pay off the jihadists to not attack the house of Saud.
That assumes that the Saudis aren't smart enough to create sovereign capital funds and invest them shrewdly.
Which is what they are, in fact, doing. Their investments don't get quite the attention given to e.g. Dubai's purchase of a stake in both the NY stock exchange and in the London exchange*, but they are out there, they are massive and they are profitable.
* except for occasional attention paid to the huge 'donations' the Sauds have given to major US universities such as Harvard, which in turn for US bases of support for Islam and apologies for terror.
turn:
"So long as we transfer treasure to the ME, the Jihad is funded."
This is so, but what then, do they do with that wealth?
They send it right back to the West, for services, and the East, for manufactured goods.
As long as the only resource they have is oil, the funding for the Jihad, while not inconsiderable, is in reality no more than what can be tolerably skimmed off the money flow.
Now once the funds are returned to the non-Islamic nations, they are distributed by the market in a far more equitable manner.
And thus the Counter-Jihad is also funded.
The net result is that if the Jihad is funded by 5 entities at 100 million dollars each, it is opposed by 500 million entities at $100 each.
And since the schwerpunkt of the Jihad is being directed from a vastly smaller set of strategists (those that write the checks), the consequences of one of them being wrong are magnified.
With a FOAF network, mistakes are not fatal to the shwerpunkt, and the chances of someone happening on a few winning strategies are multiplied.
When this occurs, a FOAF network will near-automatically reinforce successful results.
I'd offer the US state-led initiatives of tightening laws against drunk driving that occurred in the 1980's and the Concealed Weapon Permit legislations of the late 1990's for examples.
Contrast those with the failures of the Federally mandated 55mph speed limit in the 70's and the Assault Weapons Ban of the early 90's.
One area where I suspect the Jihad is extremely vulnerable is the wealth disparity of their societies. I know of no rich suicide bombers...plenty of the sons of poor men, though.
And Marx's description of Religion as being the Opium of the People may be due for a "digitally-remastered reissue",(translated into the Arabic, of course).
We in the West should certainly
know how effective those twin attacks have been, there's no reason they cannot serve again...this time, to our advantage.
That assumes that the Saudis aren't smart enough to create sovereign capital funds and invest them shrewdly.
Which is what they are, in fact, doing. Their investments don't get quite the attention given to e.g. Dubai's purchase of a stake in both the NY stock exchange and in the London exchange*, but they are out there, they are massive and they are profitable.
I think you're underestimating the extravagance and lasciviousness of these people. They may be investing their money, but that doesn't mean they still won't spend beyond their means. The Arabs are too morally bankrupt to not spend themselves back into the desert with their camels. I do agree that once the house of Saud is finished, another Islamic regime will take its place, but I also think they're going to be out of oil in a couple of decades anyway.
I've done business with the Saudis and others in the middle east. I do not underestimate anything about their culture.
A little Googling through financial news sites will make it clear that, whatever the outrageous lifestyles of the most senior royal family, the Sauds are indeed invested quite heavily and profitably in US, European and Asian sources of income for the sovereign and for personal funds. It is folly to rely on their presumed moral bankruptcy to financially exhaust them.
Bilgeman:
as far as Stalingrad is concerned: you cite the right reasons. However, the reason why the Germans stayed in the city, though the encirclement was being done, and why they were not allowed to break out to the west, once they were encircled, was Hitler's fanatical devotion to the principle that "wherever a German boot has standed, it must stay". "Fighting for every inch of soil" was Hitler's pet idea in defense. He would sometimes forbid the generals to withdraw the forces and would command them to hopeless last stands.
The expression "real warfare" was used unhappily. I did not mean that the current situation we're in is "fictional". I rather wanted to express that some people might have illusional concepts of warfare per se. The French defensive doctrine of the Maginot's line was one such case...
Pardon my English: "Stood", not "Standed". Goes away in shame :-)
Perhaps a lesser component of the infowar is to help others know more about the different countries under the curse of Islam and along with this the deep and bitter enmity that exists between Arabs at all levels. Their general nature is to not trust and this is part of their "honor/shame culture". This weakness can be exploited.
Re: Saudis, let us not forget that they are generally reviled by fellow Arabs and non-Arabs alike. The only reason they enjoy status and hobnobbing with anyone is because of their petroleum wealth. When that wealth starts to wane they will wake up to a changed world for a variety of reasons, not least of which is that countries with many thousands of service workers in KSA (Yemen, Philippines, etc.) will be able to adjust their diplomacy accordingly. Right now they have too many of us over a barrel (no pun intended). The worm will turn but will any of us be alive to witness it?
The last I heard the Arabs have enough oil reserves to go for decades, maybe 50 years or more at current use rates. Whenever it dries up won't be soon. I don't need to tell anyone here that oil is a complex subject but people forget that what they pump in Venezuela for example is just crap compared to Saudi sweet crude and requires a lot of (expensive) refinement. Doesn't Russia still have no. 1 world's reserves? And wasn't that offered as a reason they went into Afghanistan, to secure an oil route to a sea port?
The Kingdom will likely remain both secure and repressed for a long time to come. Regardless, we need to separate them and all Islamic strongholds from us. With all of their massive investments in the West and vital geopolitical considerations this may not seem possible but it is far more probable than any significant reform of Islam.
a natural
Post a Comment